1. THE SHOCKING STAT (opening hook)
“AI‑generated spear phishing emails now achieve a 54% click‑through rate compared to 12% for traditional campaigns.” (Vectra, 2025)
In plain terms: the most dangerous emails are no longer the ones full of typos and weird links. The most dangerous emails are the ones that read like your CFO wrote them—because, increasingly, a model can.
A 54% click‑through rate isn’t “more phishing.” It’s phishing that behaves like an internal memo—targeted, personalized, and timed for maximum compliance. (Vectra)
The story hidden in that number is brutal: traditional email filters were designed to catch “bad-looking” mail (known spam patterns, suspicious domains, common payloads). But spear phishing in 2026 often looks indistinguishable from normal work.
That mismatch—filters scanning for “bad,” attackers manufacturing “good”—is why inboxes keep leaking.
2. HOW WE GOT HERE (trend section)
Spear phishing didn’t suddenly become popular. It became scalable.
The post-2022 inflection point
Multiple security analyses point to a sharp acceleration in phishing volume and effectiveness after generative AI tools became widely accessible.
Phishing volume rose 1,265% from Q4 2022 to Q3 2023. (SlashNext via BRSide, 2023)
LinkedIn analysis claims phishing attack volume surged 4,151% since the launch of ChatGPT (2022). (LinkedIn analysis, 2026)
Even if you treat the 4,151% figure as directional rather than definitive (it’s not a peer‑reviewed dataset), it matches what most security teams experienced operationally: phishing became cheaper to produce, faster to iterate, and easier to personalize.
Effectiveness is rising, not just volume
Older phishing economics were limited by writing quality and research time. Spear phishing required human effort: reviewing org charts, mimicking tone, referencing real projects.
Now, attackers can generate high-quality drafts, variants, and role-based personas in minutes.
AI spear phishing improved 55% relative to human-crafted attacks between 2023 and Feb 2025. (Hoxhunt, 2025)
That “55% better than human” framing matters: filters and training were built around the assumption that humans were the best social engineers. If AI is now outperforming humans at persuasive workplace writing, then your defense must change from “spot the weirdness” to “limit who can reach you.”
The work environment makes spear phishing easier
Spear phishing thrives on ambiguity: hybrid work, vendor sprawl, and constant “quick asks.” Your inbox is a live wire of:
- new contractors
- procurement renewals
- HR policy updates
- shared docs
- login prompts
The attacker’s advantage is that modern work already resembles the tactics phishing uses.
And the bigger the email surface area, the easier it is to hide.
3. THE REAL COST (data breakdown)
Spear phishing is usually described as a security problem. The data says it’s also a time, money, and wellbeing problem—because the condition that enables spear phishing is the same condition that burns teams out: the open inbox.
Time Cost
Booher Research Institute estimates the average employee spends 2 to 2.5 hours per day on email. (Booher Research Institute)
Let’s translate that into annual life cost:
- 2.0 hours/day × 5 days/week = 10 hours/week
- 2.5 hours/day × 5 days/week = 12.5 hours/week
Over ~50 working weeks, that’s 500 to 625 hours/year inside the inbox.
That’s not “communication.” That’s a second job.
At 12.5 hours/week, email consumes ~30% of a 40-hour workweek. (Booher)
Now add spear phishing: it’s not only the time lost to actual incidents. It’s the constant micro-tax of:
- re-checking sender identities
- hovering links
- scanning for “tells”
- second-guessing payment requests
In other words, spear phishing doesn’t just steal credentials—it steals attention.
Dollar Cost
Booher’s McKinsey-style modeling estimates that for a $75,000 salary with a 1.4 benefits multiplier (≈$105,000 loaded cost), if 30% of time is spent on email, the cost is $31,500 per employee per year. (Booher)
$31,500/year per employee is the baseline inbox tax—before you even count breach costs. (Booher)
Scale that to a mid-sized organization:
- 250 employees × $31,500 ≈ $7.9M/year
- 1,000 employees × $31,500 ≈ $31.5M/year
Even if your organization’s email fraction is lower, the punchline holds: email overhead is already a multi‑million‑dollar line item. Spear phishing rides on top of that—because open inboxes create unlimited attack attempts at near-zero marginal cost.
Productivity Cost (context switching)
A widely cited finding (often attributed to UC Irvine research and popularized in productivity coverage) suggests it can take ~23 minutes to regain focus after an interruption. (D Squared citing the research lineage)
Separately, reporting on notification overload echoes that interruptions increase error rates and compress truly productive time. (Willingness, 2025)
This matters because spear phishing is designed to interrupt:
- “Urgent: invoice overdue”
- “Action required today”
- “Security alert: sign-in attempt”
Even when employees don’t click, the email still triggers a cognitive fork: Is this real? Should I escalate? That decision moment is itself an interruption.
And spear phishing doesn’t need you to click every time. At scale, it only needs a few clicks from the most overloaded people.
Mental Health Cost
The workforce isn’t merely distracted; it’s strained.
A “Digital Anxiety” synthesis article points to research linking continuous notifications to activation of the stress response (HPA axis), elevated cortisol, sleep disruption, and cognitive impairment. (LinkedIn “Digital Anxiety” analysis)
Meanwhile, mass-market surveys (with quality caveats) claim:
- 57% of workers feel overwhelmed by admin duties; 46% have considered quitting due to the burden. (Fyxer via The Sun, Feb 2026)
- A US counterpart claims 50% considered quitting; 59% work beyond contracted hours weekly; nearly 2 hours/day on email. (NY Post, 2026)
These aren’t perfect academic instruments, but they align with what inbox-driven work feels like: you’re never done, only caught up for a moment.
And spear phishing weaponizes that state. Fatigued people make faster decisions, rely on heuristics, and comply with authority cues.
Spear phishing succeeds not just because it’s convincing—but because recipients are busy, interrupted, and trained to act fast.
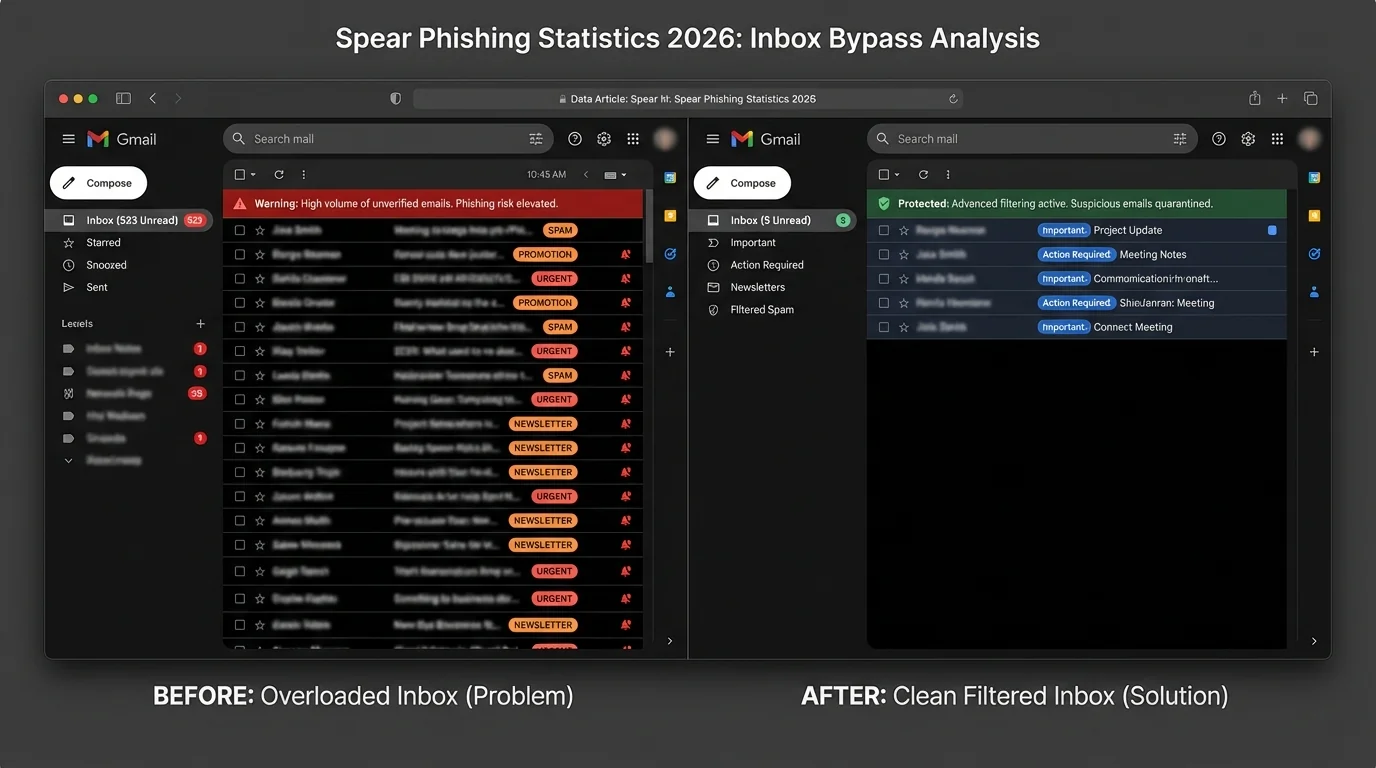
Why attacks bypass traditional email filters in 2026
Traditional filtering is fundamentally probabilistic: it guesses what’s bad based on patterns.
Spear phishing in 2026 is engineered to avoid patterns.
Here are the main bypass mechanisms—explained as methodology failures, not “one vendor did X.”
1) Language is no longer a tell
Older filters and user training benefited from obvious signals: broken grammar, unnatural phrasing, broad greetings.
But Vectra’s click-rate gap—54% AI vs 12% traditional—is a proxy for a deeper change: high-quality writing is now cheap. (Vectra)
Attackers can match:
- your company’s tone
- the recipient’s role
- the urgency style of internal comms
So filters that weight “odd language” as a risk indicator lose signal.
2) Personalization breaks pattern matching
The more specific the email is, the less it resembles known phishing templates.
Hoxhunt’s reported 55% improvement suggests AI-generated attacks are not just better written—they’re better targeted and iterated. (Hoxhunt)
That creates “unique snowflake” phishing: many small variants instead of one mass blast. Filters trained on bulk similarity struggle when every message is slightly different.
3) The attack surface is bigger than the filter’s model of “trust”
Most organizations run on constant external email:
- vendors
- candidates
- customers
- partners
- inbound leads
This creates a structural problem: filters have to allow huge amounts of unknown senders because business requires it.
So the filter’s job becomes impossible: let in enough outsiders to keep revenue moving, but keep out the one outsider who’s a criminal.
That’s why open inbox is a design flaw, not a user flaw.
4) “Looks like a workflow” beats “looks like malware”
Modern spear phishing often isn’t a zip file with a virus. It’s:
- a link to a realistic login page
- a request to update banking details
- a fake DocuSign-style prompt
In other words: social engineering that impersonates normal operations.
Filters are better at catching bad payloads than bad intent.
5) Decision fatigue is the stealth bypass
Even a good filter is not perfect. Once a few spear phishing emails reach the inbox, the recipient becomes the final classifier.
But the data on email time (2–2.5 hours/day) implies people are already operating under heavy cognitive load. (Booher)
In that environment, the attacker doesn’t need to beat your security team. They need to beat your Tuesday at 4:47 PM.
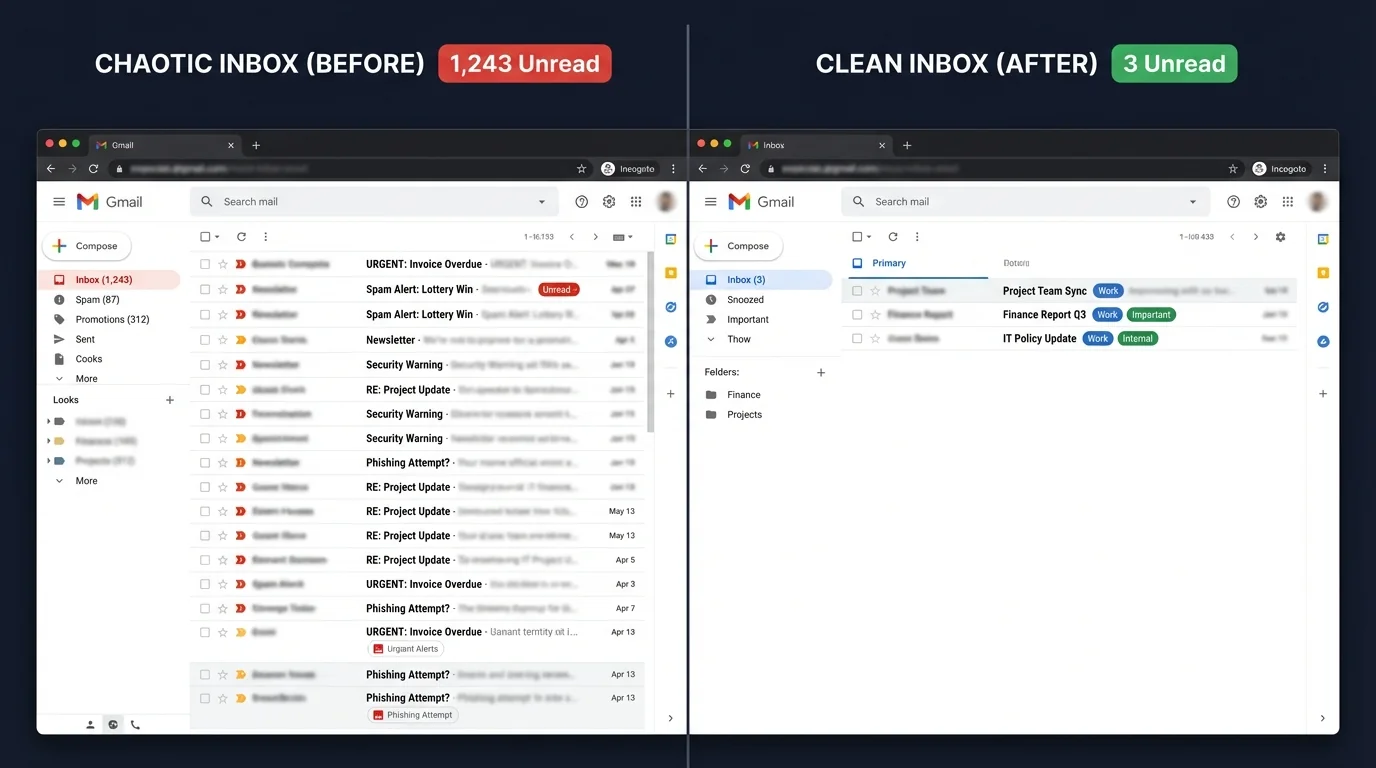
4. THE SOLUTION (tie to KeepKnown)
If spam filters are failing because they guess what’s bad, then the inversion is simple:
Stop guessing. Decide who’s allowed.
This is the KeepKnown philosophy: the “open inbox” is a failed concept. In 2026, letting strangers reach employees by default is equivalent to letting strangers walk into your office building and shout requests.
The KeepKnown Protocol: strict allow-listing
KeepKnown is an API-based email filter that works at the server level (not a plugin). It moves non-contacts into a separate label/folder: “KK:OUTSIDERS.”
Mechanically, this changes the game:
- Traditional filters: attempt to classify every inbound email as good/bad.
- Strict allow-listing: only prioritizes mail from known-good relationships (contacts), and routes unknowns away from the primary attention stream.
This doesn’t claim, “outsiders are malicious.” It claims something more operationally true:
Outsiders are unverified, and unverified messages shouldn’t compete with verified relationships for attention.
How strict allow-listing addresses the data-proven costs
1) Time: Fewer inbox decisions
When unknown senders stop landing in the main inbox, you reduce micro-triage. Remember: with email already costing 500–625 hours/year, shaving even a small fraction is meaningful. (Booher)
2) Money: Reduce the $31,500 “inbox tax” component that is pure sorting
Booher’s modeled $31,500/year per employee isn’t destiny; it’s the cost of an inbox that mixes high-trust and zero-trust mail in one stream. (Booher)
3) Productivity: Fewer interruptions
If interruptions can take ~23 minutes to recover from, then the best interruption is the one that never happens. (D Squared / UC Irvine lineage)
4) Security: Less exposure to the highest-performing attack class
Spear phishing wins by reaching the inbox and looking normal. Strict allow-listing reduces how often “unknown normal-looking” emails are seen at all.
Why allow-listing beats “AI sorting” for spear phishing
Methodologically, AI sorting is still guessing—just with better guesses.
But spear phishing is an adversarial problem: attackers adapt to the classifier. As language models improve, AI sorting systems face a treadmill: ever more convincing emails, ever harder detection.
Strict allow-listing sidesteps the treadmill by changing the default:
- You don’t need to perfectly detect spear phishing.
- You need to minimize untrusted reach.
For teams using Outlook or Gmail, KeepKnown can coexist with existing security layers, adding a behavioral control: who gets immediate access to humans.
If you want implementation details for specific platforms, see:
- How to Set Up a Contact Only Email Filter in Gmail
- How to Configure Strict Allow Listing in Outlook 365
- AI Email Sorting vs Whitelisting for Inbox Control
More on the product: https://keepknown.com (free trial available).
5. WHAT HAPPENS NEXT (future outlook)
If nothing changes
The trend lines imply three compounding forces:
1) More attempts (volume growth) (SlashNext)
2) Higher-quality lures (effectiveness growth) (Hoxhunt, Vectra)
3) More cognitive overload (2–2.5 hours/day email + interruptions) (Booher; attention research lineage)
In that world, “security awareness training” becomes a fragile strategy: it asks tired humans to beat industrialized persuasion at scale.
With intervention: inbox design becomes a security control
The strongest prediction you can make from the data is not about which lure will work next year.
It’s about where attackers will keep aiming: the primary inbox, because it’s still the fastest path to a human.
So the intervention that scales is structural:
- reduce who can reach the primary inbox
- move unknown senders out of the main attention channel
- make “trust” the first sorting rule
That’s what strict allow-listing operationalizes.
Spear phishing is winning because it’s “normal-looking.” The counter is making “unknown” non-urgent by default.
Source notes (quality and caveats)
- Vectra / Hoxhunt / SlashNext: reputable security vendors; useful directional data, but methodologies can vary.
- LinkedIn analyses / viral metrics (e.g., 4,151%): treat as indicative rather than definitive.
- Booher Research Institute: productivity modeling; assumptions should be adapted per org.
- Notification/cortisol syntheses: useful for understanding mechanism; best used alongside peer-reviewed attention research.
Even with caveats, the signals converge: phishing is scaling and improving faster than inbox defenses built on guessing.